Key Takeaways
- The DUPH-BAAC scheme employs a multi-step process for initializing keys, encrypting data, and managing access policies.
- It integrates blockchain technology for secure key management and dynamic attribute updates, enhancing data accessibility while maintaining security.
- Verification mechanisms ensure that only authorized users can decrypt and access encrypted data through computed identities and attribute sets.
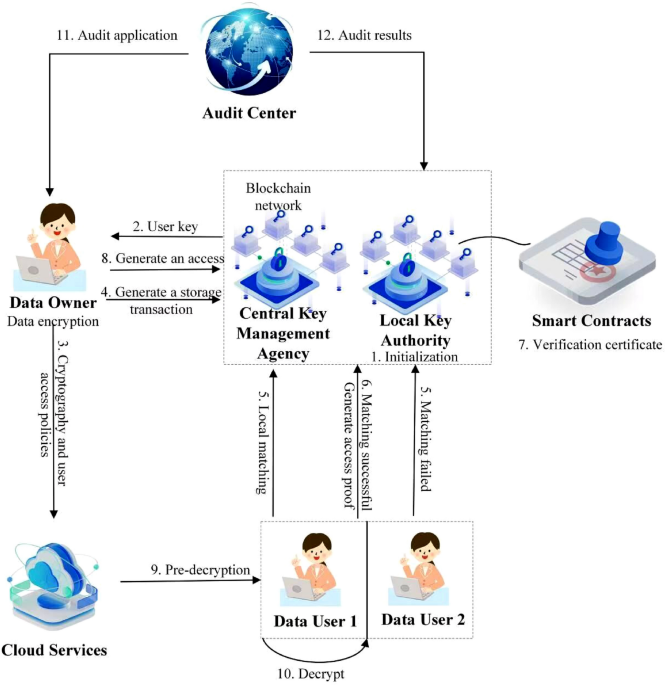
The DUPH-BAAC scheme presents an advanced framework for managing encryption and access control in digital environments, utilizing blockchain technology for enhanced security and efficiency. The system is structured around six primary processes: initialization, user identity key generation, data encryption, ciphertext generation, access control policy management, and decryption.
**System Initialization** involves setting up the Central Key Management Authority (CKA) within a blockchain system, wherein a global public key (GP) is created, accompanied by the establishment of static attribute definitions. The initialization leverages bilinear group selection and the definition of hash functions.
Following this, the Local Key Authority (LKA) produces user-specific public and private keys, ensuring that attributes are dynamically managed within a designated range. Each user’s identity key (UK_UID) is generated through a set of mathematical inputs, combining user attributes with the global public key.
**Data Encryption** is executed by the data owner, who inputs essential parameters, including user identification and ciphertext structures, to output the ciphertext (D). Each encrypted file correlates to a unique ciphertext address that signifies storage within the blockchain network.
Another key element is **Access Control and Policy Hiding**. Once ciphertext is stored with an embedded policy, it undergoes an intricate broadcast and verification process within the blockchain. This ensures robust access control by requiring users to prove their eligibility through attribute matching supported by cryptographic proofs.
**Ciphertext Decryption** is divided into two stages. First, a cloud server must ascertain compliance with the user’s access permissions against the ciphertext attributes. If both verifications succeed, the server employs a proxy decryption process that produces intermediate ciphertext (D’). Subsequently, local decryption by the user transforms this intermediate ciphertext back into plaintext.
To accommodate changes in user attributes, the scheme also includes an **Attribute Update** mechanism, which adjusts both user keys and ciphertexts in real time according to the updated attributes managed by the LKA.
Lastly, the **Ciphertext Verification** process ensures integrity by employing arithmetic validation methods. This step confirms the correctness and security of the ciphertext, determining if the decryption process is passed or failed.
The DUPH-BAAC scheme thus showcases a comprehensive framework for encryption, access management, and user identity verification, leveraging blockchain capabilities for security and dynamic adaptability to user needs.
The content above is a summary. For more details, see the source article.