Key Takeaways
- Over 700,000 attacks were recorded against a designed smart farming ecosystem using a honeypot server, primarily originating from China, the U.S., and Russia.
- Attackers commonly sought to exploit TCP and UDP services, employing tactics like port scanning, brute-force attacks, and malware delivery.
- Effective security measures, such as changing default credentials and regularly updating software, are essential to protect against these cyber threats.
Analysis of Cyber Threat Intelligence Data
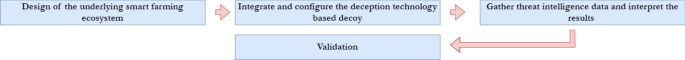
The T-Pot honeypot server was developed to draw in cyber attackers by simulating a network of vulnerable services. Throughout the data collection period, which has accumulated over 700,000 recorded attempts, various attack types emerged, including port scans and exploit attempts aimed at breaching a smart farming ecosystem.
The recorded attacks highlighted several patterns, with a significant surge noted mid-observation, attributed to increased interaction from cyber criminals probing the honeypot for vulnerabilities. Insights from the data revealed that a large percentage of attacks originated from countries like China, the United States, and Russia, largely due to their technological advancements and extensive internet infrastructures.
A breakdown of the attack types found that many focused on TCP and UDP services, indicating a targeted effort to exploit widely used protocols. Attackers often engaged in reconnaissance to collect information about the target environment, followed by attempts to deliver malware or conduct denial-of-service attacks.
Tables and figures referenced identify the most frequently targeted ports (like 80 for HTTP and 22 for SSH) and outline the origin of attacks by country and IP address reputation. Notably, the majority of username and password attempts were standard defaults set by service providers, emphasizing the ease with which attackers can gain access if such credentials are not changed.
The validation of the threat intelligence data was conducted with a Raspberry Pi setup, confirming similar vulnerability patterns to those observed with the T-Pot system. This secondary experiment generated more than 56,000 unauthorized access attempts in a three-week period, with parallels in the nature of attacks received.
The data underscores critical vulnerabilities, particularly the reliance on default usernames and passwords and the prevalence of unprotected open ports. Recommendations include the regular updating of security measures, encouraging strong credential practices, and implementing more robust network monitoring.
The collaboration among all stakeholders—including farmers, solution providers, and government entities—is essential for establishing a secure smart agricultural framework. The establishment of clear security regulations and practices is crucial in addressing the rising threat landscape facing smart farming technologies, ensuring not only operational safety but also broader data integrity within the agricultural sector.
The content above is a summary. For more details, see the source article.