Key Takeaways
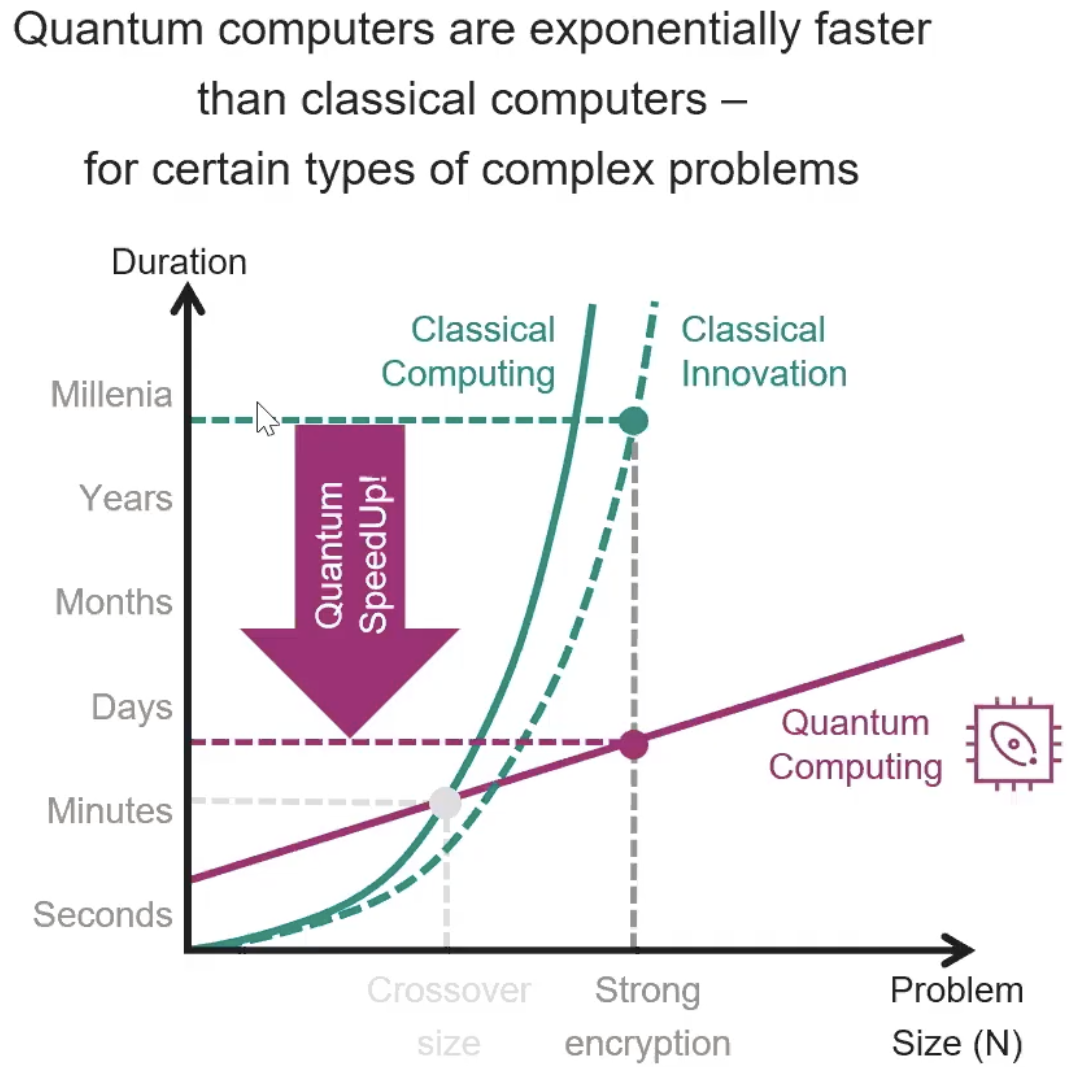
- Quantum computers are projected to break current encryption algorithms within the next decade.
- These advancements may enable quantum computers to decrypt sophisticated encryption in minutes.
- Erik Wood from Infineon discusses the implications for chip design and computer architectures.
Emerging Threat of Quantum Computing to Cybersecurity
Quantum computing is no longer confined to the realm of science fiction; it is poised to become a commercial breakthrough that could revolutionize cybersecurity. Experts predict that within the next ten years, quantum computers will have the capability to undermine virtually all encryption algorithms in circulation today. This technological evolution raises significant concerns over data security, as encryption methods deemed unbreakable for over a century might be compromised in mere minutes.
Erik Wood, senior director of cryptography and product security at Infineon, highlights the transformative nature of cryptographically relevant computers. Current encryption methods rely heavily on mathematical complexities that are labor-intensive for classical computers to solve. However, the principles governing quantum computing leverage quantum bits, or qubits, which can represent multiple states simultaneously. This allows quantum computers to perform calculations at speeds unthinkable with traditional systems.
The potential ramifications of this technology extend beyond just breaking encryption. As quantum computing becomes more mainstream, the underlying architectures of computers and the design of chips will likely need significant adaptations to accommodate new computational methods. This evolution will require a collaborative effort from various sectors, including hardware manufacturers, software developers, and cybersecurity experts, to create solutions that can withstand the capabilities of quantum computers.
While the timeline for commercial quantum computing is still unfolding, the urgency for industries to adapt is clear. Organizations must begin exploring quantum-resistant encryption techniques to safeguard their data against potential future breaches. Wood emphasizes the importance of proactive measures; waiting until quantum computers become operational is not a viable strategy for protecting sensitive information.
In summary, the advent of quantum computing presents both unprecedented opportunities and daunting challenges for cryptography and data security. As this technology progresses, proactive planning and adaptation will be essential in maintaining the integrity of data and systems worldwide.
The content above is a summary. For more details, see the source article.